Read our latest thinking, ideas, and opinions…
For years, one of the most reliable tools in network defense has been the IP blocklist — a list of known malicious addresses that get flagged or blocked before they can do damage. If an attack comes from a suspicious address, you block it. If a…
Picture a deal team negotiating a major acquisition. Calls between executives and counsel flying back and forth on mobile devices. Every message encrypted. Every call secured — or so the security stack indicates.
Most people picture mobile surveillance the same way: a target clicks a malicious link, spyware installs, and an attacker gains access. It's a tidy mental model. It's also increasingly incomplete.
In January 2025, WhatsApp notified approximately 90 users that their devices had been targeted with Graphite, a surveillance tool developed by Israeli firm Paragon Solutions. The targets included journalists, humanitarian workers, and civil society…
Practical guidance for CISOs to build enterprise-wide mobile security programs that stand up to advanced spyware and surveillance threats.
Why mobile compromise looks different for high-profile users When an executive or senior official asks, "How would I know if my phone was hacked?" they are rarely looking for a deep dive into vulnerability identifiers. They want a clear mental model…
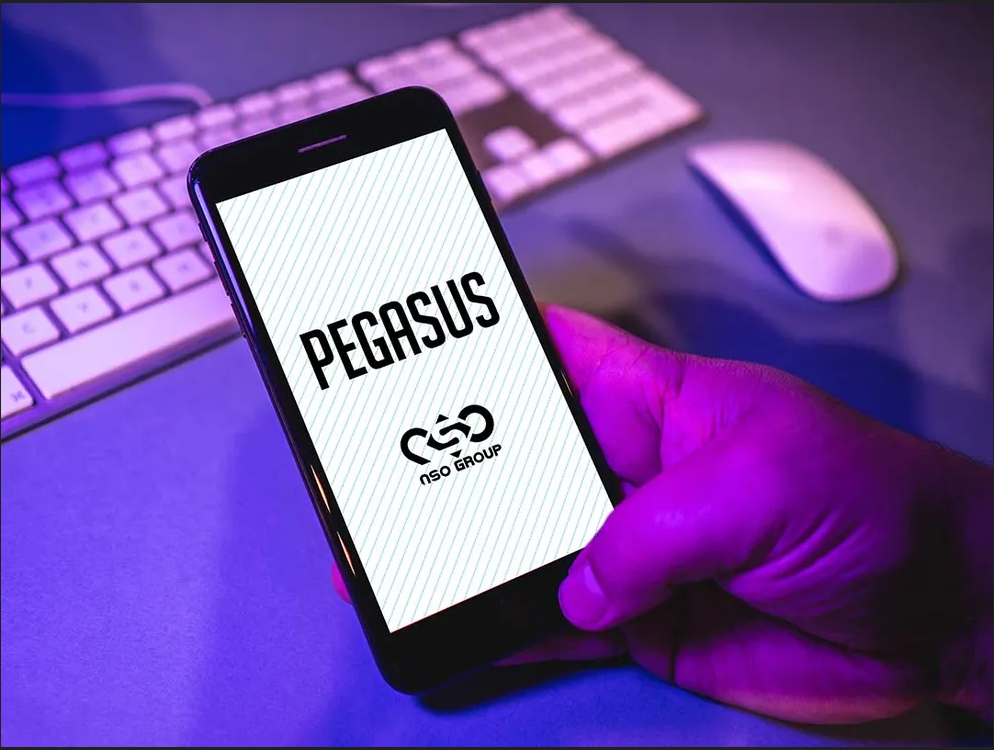
How Pegasus-class spyware differs from commodity malware The first step in defending against Pegasus-style spyware is to understand what it is—and what it is not. Pegasus, developed by NSO Group, is a class of mobile spyware designed to compromise…
Mobile communication has changed dramatically over the past decade—and so have the risks that come with it. Conversations happen across multiple apps, devices and networks, all of which often leave behind metadata and patterns that can be just as…
With over two billion users worldwide, WhatsApp has become the default messaging platform for personal and increasingly, professional communications. Its ubiquity offers convenience, but for those with genuinely sensitive information to protect,…